A new dangerous content injection vulnerability has been discovered in the WordPress CMS, it is a zero-day content injection flaw in the WordPress REST API.
A fix for this was silently included on version 4.7.2 along with other less severe issues.
Introduction
This privilege escalation vulnerability affects the WordPress REST API that was recently added and enabled by default on WordPress 4.7.0 or 4.7.1. If your website is on these versions of WordPress then it is currently vulnerable to this bug.
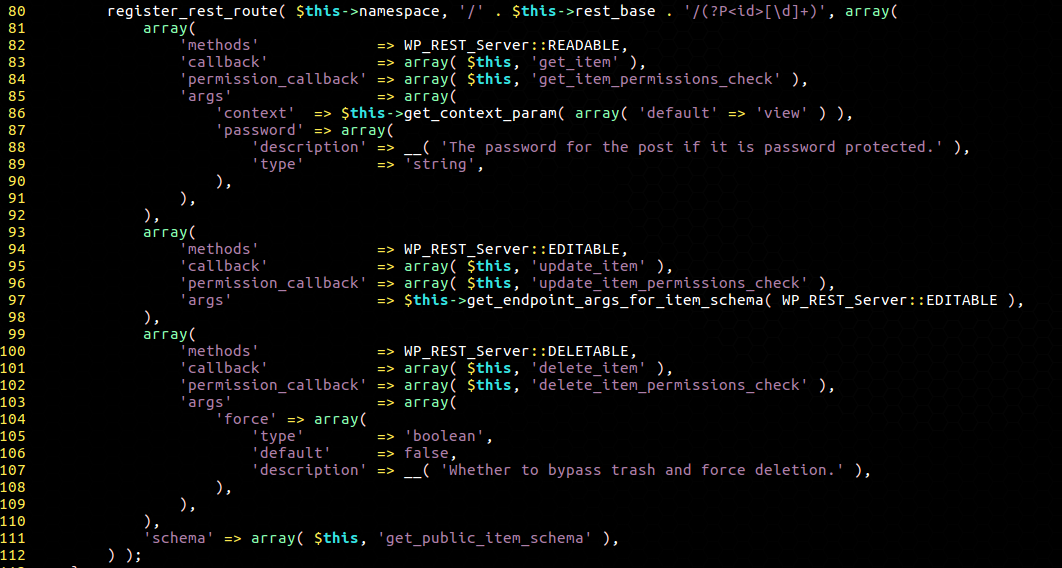
The vulnerability is easy to exploit and affects versions 4.7.0 and 4.7.1 of the WordPress content management system (CMS), allowing an unauthenticated attacker to modify all pages on unpatched sites and redirect visitors to malicious exploits and a large number of attacks.
The impact of the flaw is severe, at least 18 million websites run the popular WordPress CMS, roughly 26% of the top 10,000 websites are running WordPress.
In Conclusion
Administrators that have not enabled automatic updates on their website need to update it as soon as possible.
Websites that using Malware Expert – ModSecurity rules are protected against this threat.
Read more details Sucuri.
