In this article I’m going to discuss how to find and Whitelist specific ModSecurity rules that might be causing 406 errors on your websites on either your VPS (Virtual Private Server) or dedicated server.
The rules that ModSecurity uses can help block potential attack attempts from malicious users upload malware to servers, but sometimes it can also block legitimate upload requests, and knowing how to go in and find what rules are getting triggered and how to whitelist them can be handy.
All-in-One WP Migration
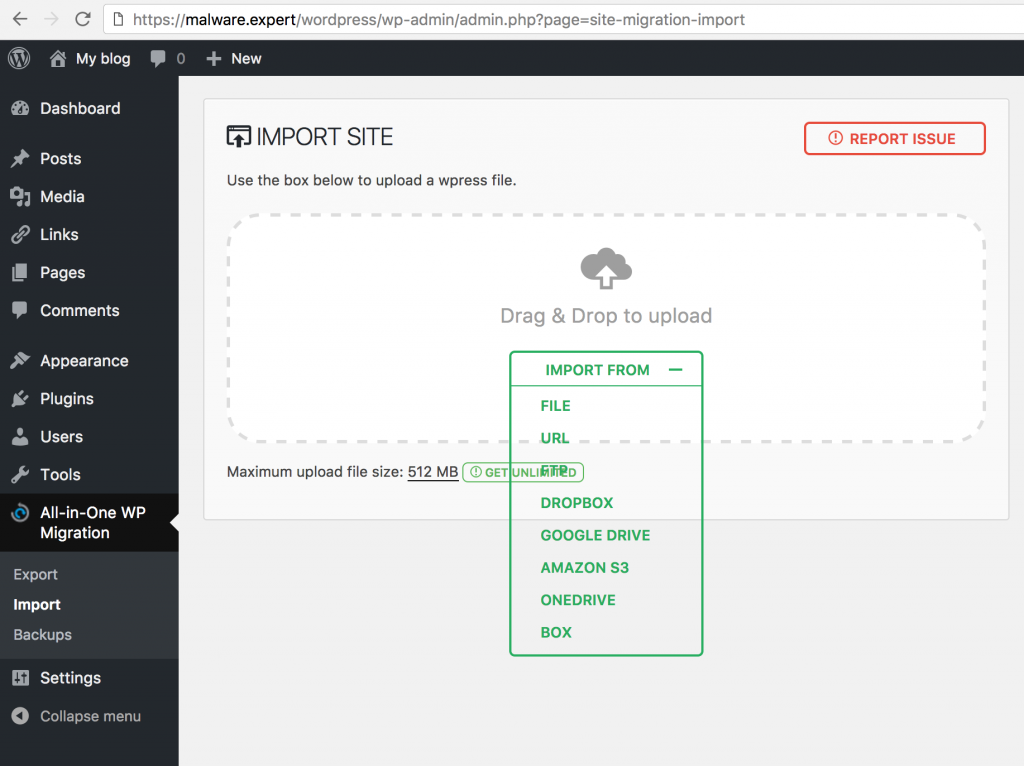
This tutorial we using WordPress with All-in-One WP Migration plugins, that allow import/export your WordPress installation to any server.
Sometimes this cause false/positive alarms with ClamAV scanner with Malware rules.
Apache error.log
First we need find ModSecurity rule that blocking upload to server. This usually found in Apache error.log or if shared webhosting environment then domain error.log.
Our tutorial this is very easy search error code: Access denied with code 406
That rule is in /etc/modsecurity.d/runav.conf file.
[Wed Feb 22 10:47:36.458459 2017] [:error] [pid 32046] [client 127.0.0.1:62090] [client 127.0.0.1] ModSecurity: Access denied with code 406 (phase 2). File "/tmp/20170222-104655-WK1P-1Qikx4AAH0um30AAAA6-file-U3UJSa" rejected by the approver script "/usr/local/bin/runav.pl": 0 clamscan: {HEX}Malware.Expert.generic.malware.6.UNOFFICIAL [file "/etc/modsecurity.d/runav.conf"] [line "14"] [id "950115"] [msg "Virus found in uploaded file"] [severity "CRITICAL"] [hostname "malware.expert"] [uri "/wordpress/wp-admin/admin-ajax.php"] [unique_id "WK1P-1Qikx4AAH0um30AAAA6"], referer: https://malware.expert/wordpress/wp-admin/admin.php?page=site-migration-import
ClamAV scanner rule
If we look better this rule, it’s typically ModSecurity scanning rule:
SecRule FILES_TMPNAMES "@inspectFile /usr/local/bin/runav.pl" \ "phase:2,t:none,block,msg:'Virus found in uploaded file',id:'950115'"
Now we need find POST payload that we can make Whitelist rule for that.
POST payload
When we try import old WordPress site with All-in-One WP Migration, we get this POST payload and filed import.
--dd5ec022-A-- [22/Feb/2017:10:47:36 +0200] WK1P-1Qikx4AAH0um30AAAA6 127.0.0.1 62090 127.0.0.1 443
--dd5ec022-B-- POST /wordpress/wp-admin/admin-ajax.php?action=ai1wm_import HTTP/1.1 Host: testi0.zoner.fi Connection: keep-alive Content-Length: 4624901 Origin: https://testi0.zoner.fi User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_12_3) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/55.0.2883.95 Safari/537.36 content-type: multipart/form-data; boundary=----WebKitFormBoundarypzt79sF4w2tJ9mLL Accept: */* Referer: https://malware.expert/wordpress/wp-admin/admin.php?page=site-migration-import Accept-Encoding: gzip, deflate, br Accept-Language: en-US,en;q=0.8 Cookie: * --dd5ec022-C--
--dd5ec022-F-- HTTP/1.1 406 Not Acceptable Content-Length: 284 Keep-Alive: timeout=2, max=99 Connection: Keep-Alive Content-Type: text/html; charset=iso-8859-1
--dd5ec022-H--
Message: Access denied with code 406 (phase 2). File "/tmp/20170222-104655-WK1P-1Qikx4AAH0um30AAAA6-file-U3UJSa" rejected by the approver script "/usr/local/bin/runav.pl": 0 clamscan: {HEX}Malware.Expert.generic.malware.6.UNOFFICIAL [file "/etc/modsecurity.d/runav.conf"] [line "14"] [id "950115"] [msg "Virus found in uploaded file"] [severity "CRITICAL"]
Apache-Error: [file "apache2_util.c"] [line 271] [level 3] [client %s] ModSecurity: %s%s [uri "%s"]%s
Action: Intercepted (phase 2)
Apache-Handler: application/x-httpd-php
Stopwatch: 1487753215267371 41258574 (- - -)
Stopwatch2: 1487753215267371 41258574; combined=277262, p1=4393, p2=272864, p3=0, p4=0, p5=4, sr=261, sw=1, l=0, gc=0
Producer: ModSecurity for Apache/2.9.1 (http://www.modsecurity.org/).
Server: Apache/2
Engine-Mode: "ENABLED"
--dd5ec022-Z--
SecMarker
We need ModSecurity SecMarker directive to whitelist specified rule that block Apache Upload scan.
Write Whitelist ModSecurity rule
Now we have very easy write ModSecurity whitelist rule to WordPress All-in-One WP Migration plugin. First we create rule that catch POST Payload and skip orginal rule if found:
Whitelist rule
SecRule REQUEST_METHOD "POST" "id:950100,phase:2,t:none,chain,pass,skipAfter:IGNORE_CLAMAV_SCAN,nolog,msg:'Malware expert - All-in-One WP Migration'" SecRule REQUEST_URI "@contains /wp-admin/admin-ajax.php?action=ai1wm_import" "t:none,t:lowercase,t:urldecode,nolog"
Orginal rule
SecRule FILES_TMPNAMES "@inspectFile /usr/local/bin/runav.pl" \ "phase:2,t:none,block,msg:'Virus found in uploaded file',id:'950115'"
skipAfter rule
SecMarker IGNORE_CLAMAV_SCAN
Final words
There is another ways also remove rules, example SecRuleRemoveById, but is simple and if you need get more whitelist rules, just add them before Orginal rule. And here, you can find more ModSecurity Rule Examples.
Check out:
Malware Expert – Free Malware Signatures
Malware Expert – ModSecurity Rules
