The vulnerability – High severity vulnerability fixed in WordPress Elementor Pro plugin
As many of you are aware already, there is a critical vulnerability reported in the WordPress Elementor Pro plugin, which is installed on millions of websites. Though they have already released a patched version already, there are still many websites left unpatched, and active attack campaigns are going on against the WordPress websites. The vulnerability, which impacts version 3.11.6 and all older versions, allows logged-in normal users, like customers or site members, to change the website settings, create new admin users, change the site URL, etc.
What did we notice about this attack campaign?
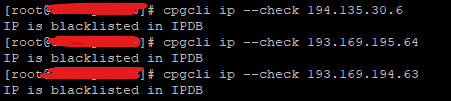
Based on some reliable sources, most of the attack campaigns were started from the following IPs:
Upon investigating this further and checking the logs, we have noticed some attack attempts since 24th March 2023 and our WAF was blocking them without any specific rule added for this particular vulnerability ( our WAF rules are so generic to block many of the common abuse attempts ).
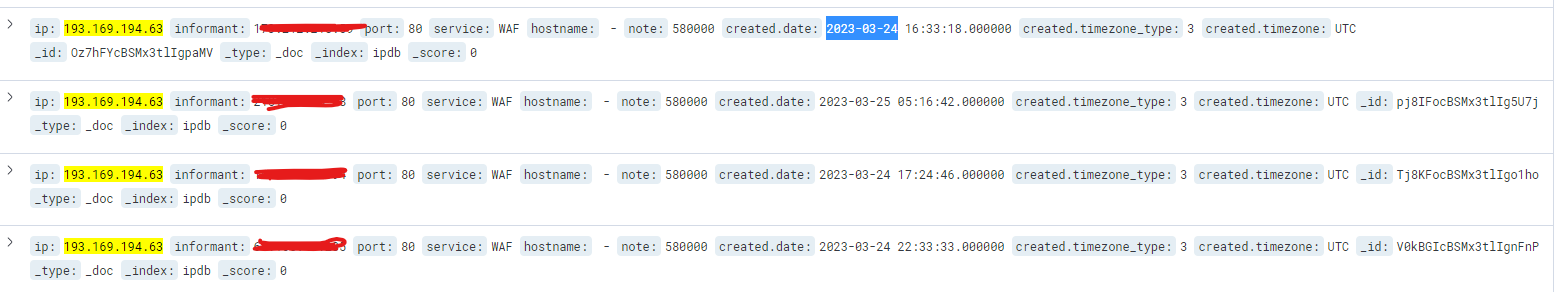
After multiple attack attempts against the servers within the cPGuard network, the IPDB system has caught it on the central system and blocked on all client servers where IPDB is enabled. Given below are a few relevant screenshots of the given incidents.
So what else we did do to protect servers from this vulnerability?
Even if we found that the automated attack attempts are already being blocked by the WAF and IPDB, we have released a WAF update today specifically to block exploiting this vulnerability specifically. We are still monitoring the servers and logs and we will amend the WAF rules as we get more pieces of evidence and logs.
It is also recommended to advise your customers and update the plugin to version 3.11.7 or higher as it is available.

