The b374k shell is a popular PHP-based web shell that is used by attackers to gain unauthorized access and control over web servers. Like many web shells, it provides a range of functionalities that allow attackers to interact with the compromised server.
b374k shell key features
Here are some key characteristics and features of the b374k shell:
- Stealthy: b374k is known for its stealthy features. It is designed to be inconspicuous and difficult to detect. Attackers may use various obfuscation techniques to hide the presence of the shell.
- User-Friendly Interface: It offers a user-friendly web-based interface that makes it relatively easy for attackers to navigate and control the compromised server. The interface includes features like file management, command execution, and database interaction.
- Remote Code Execution: Attackers can use the b374k shell to execute arbitrary code on the server. This allows them to run system commands and perform actions such as uploading and downloading files, creating directories, and manipulating data.
- File Management: The shell provides file management capabilities, allowing attackers to browse, view, edit, upload, and delete files on the server. This can be used to plant malicious files or modify existing ones.
- Security Bypass: b374k may attempt to bypass security mechanisms and restrictions on the server to gain elevated privileges and evade detection. This can include exploiting vulnerabilities or misconfigurations in the server software.
- Database Interaction: It can interact with databases, enabling attackers to access and manipulate database contents, potentially exposing sensitive information.
- Information Gathering: The shell can gather information about the server’s configuration, environment, and software stack, which can be valuable for further attacks or reconnaissance.
- Customization: b374k is often customizable, allowing attackers to modify its appearance and functionality to suit their specific needs and objectives.
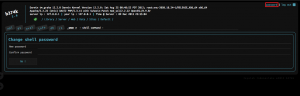
- Password Protection: Some versions of b374k may include password protection to restrict access to authorized users only. Attackers typically attempt to bypass or crack these passwords.
More on the b374k-shell
Source code and latest version: https://github.com/b374k/b374k
Older version: http://code.google.com/p/b374k-shell
Other webshells also: https://github.com/JohnTroony/php-webshells