PHP backdoors are server-side malicious scripts. The typical examples of such backdoors are various File Managers, Web Shells, Command Shells, tools for bypassing admin login, or various one-purpose scripts allowing the attacker to upload and run another type of malicious scripts. The payload is PHP-based, thus intended for server-side use and the payload is executed directly on the server, while the site is loaded. Only the payload result (such as the Web Shell environment) is visible in the browser, not the malicious code itself. It’s very common, that backdoors don’t have any visible signs in the site code and it’s impossible to detect them by accessing the infected site from outside. Server-level analysis is necessary in case of infection by this type of malware.
They allow the attacker to browse, edit, download or upload files placed on the server comfortably from the browser. In most cases, they’ve got a comprehensible Graphical User Interface so even attackers without any deep computer skills are able to effectively work with them. There are also advanced File Managers with many more features implemented such as packing functions (e.g. zip), network tools, and shells.
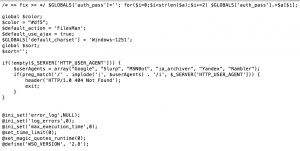
FilesMan is the most commonly used hacking tool for customer website. We found a new version of hello.php (packed) and crc validation of that file: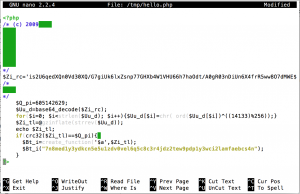
When we unpacked this hello.php we found inside that file Filesman Shell:
We updated malware.expert signatures to found this also!
References: https://kb.sucuri.net/malware/signatures/php.backdoor.filesman.002.006